搜索结果: 1-15 共查到“efficiently”相关记录49条 . 查询时间(0.116 秒)

New technology will allow important metals to be made more efficiently
metallic oxide thin film electronic components
2021/8/9
Researchers have invented a cheaper, safer, and simpler technology that will allow a 'stubborn' group of metals, such as the Pt-group elements, to be transformed into thin films for various practical ...
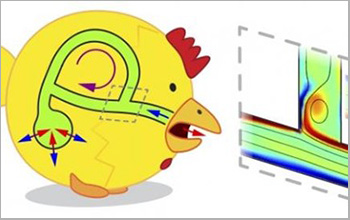
How do birds breathe so efficiently? Looped airways facilitate air flows(图)
birds breathe efficiently Looped airways facilitate air flows
2021/4/9
Birds breathe with greater efficiency than humans because of the structure of their lungs --looped airways that facilitate air flows that go in one direction -- a team of researchers has found. The re...
We present modifications to the MPC system SCALE-MAMBA to enable the evaluation of garbled circuit (GC) based MPC functionalities and Linear Secret Sharing (LSSS) based MPC functionalities along side ...
Efficiently Masking Binomial Sampling at Arbitrary Orders for Lattice-Based Crypto
Masking Post-quantum Cryptography
2019/8/8
With the rising popularity of lattice-based cryptography, the Learning with Errors (LWE) problem has emerged as a fundamental core of numerous encryption and key exchange schemes. Many LWE-based schem...
Subversion in Practice: How to Efficiently Undermine Signatures
cryptanalysis digital signatures implementation
2018/12/19
Algorithm substitution attack (ASA) on signatures should be treated seriously as the authentication services of numerous systems and applications rely on signature schemes and compromising them has a ...
Fast Scalar Multiplication for Elliptic Curves over Prime Fields by Efficiently Computable Formulas
twisted Edwards curves Edwards curves scalar multiplication
2018/11/6
This paper addresses fast scalar multiplication for elliptic curves over finite fields. In the first part of the paper, we obtain several efficiently computable formulas for basic elliptic curves arit...
Public-Key Encryption Resistant to Parameter Subversion and its Realization from Efficiently-Embeddable Groups
Public-key encryption subversion mass surveillance
2018/1/11
We initiate the study of public-key encryption (PKE) schemes and key-encapsulation mechanisms (KEMs) that retain security even when public parameters (primes, curves) they use may be untrusted and sub...
The Strength of Weak Randomization: Efficiently Searchable Encryption with Minimal Leakage
efficiently searchable encryption encrypted databases
2017/11/13
Efficiently searchable and easily deployable encryption schemes enable an untrusted, legacy service such as a relational database engine to perform searches over encrypted data. The ease with which su...
Fast Scalar Multiplication for Elliptic Curves over Binary Fields by Efficiently Computable Formulas
binary elliptic curves point multiplication lambda coordinates
2017/9/7
This paper considers efficient scalar multiplication of elliptic curves over binary fields with a twofold purpose. Firstly, we derive the most efficient 3P3P formula in λλ-projective coordinates and 5...

Catalysts Developed at Carnegie Mellon Efficiently and Rapidly Remove BPA from Water(图)
Catalysts Carnegie Mellon Rapidly Remove BPA Water
2017/9/1
Carnegie Mellon University chemist Terrence J. Collins has developed an approach that quickly and cheaply removes more than 99 percent of bisphenol A (BPA) from water. BPA, a ubiquitous and dangerous ...
Determining the Nonexistent Terms of Non-linear Multivariate Polynomials: How to Break Grain-128 More Efficiently
Stream ciphers Grain-128 Polynomial reduction
2017/5/15
In this paper, we propose a reduction technique that can be used to determine the density of IV terms of a complex multivariable boolean polynomial. Using this technique, we revisit the dynamic cube a...
CWRU researchers directly measure how perovskite solar films efficiently convert light to power
CWRU researchers directly measure perovskite solar films convert light to power
2017/2/16
Solar cells made with films mimicking the structure of the mineral perovskite are the focus of worldwide research. But only now have researchers at Case Western Reserve University directly shown the f...
The Reason Why Some Divide-and-Conquer Algorithms Cannot Be Efficiently Implemented
divide-and-conquer algorithm data expansion merge sort
2016/12/8
In the literature there are some divide-and-conquer algorithms, such as
Karatsuba’s algorithm and Strassen’s algorithm, which play a key role in analyzing the
performance of some cryptographic proto...
We device a general secret sharing scheme for evolving access structures (following [KNY16]). Our scheme has (sub)exponentially smaller share complexity (share of ii'th party) for certain access struc...


