搜索结果: 1-15 共查到“LWE”相关记录137条 . 查询时间(0.06 秒)
Revisiting the Hybrid attack on sparse and ternary secret LWE
Lattice-based Cryptography Learning with Errors Homomorphic Encryption
2019/9/16
In the practical use of the Learning With Error (LWE) based cryptosystems, it is quite common to choose the secret to be extremely small: one popular choice is ternary (±1,0±1,0) coefficient vector, a...
近年来,量子计算机技术发展迅速,它对传统公钥密码算法的安全性带来了潜在的巨大威胁。因此,美国、中国、欧盟等世界主要国家和地区纷纷开始研制抗量子计算机攻击的密码算法。其中,美国国家标准与技术研究院(National Institute of Standards and Technology,NIST)于2016年面向全球征集抗量子密码算法标准,并于2017年底完成了首轮候选算法的征集工作。
A hash function family is called correlation intractable if for all sparse relations, it hard to find, given a random function from the family, an input output pair that satisfies the relation. Correl...
Module-LWE versus Ring-LWE, Revisited
Lattice-based Cryptography Security Reduction Cyclotomic Fields
2019/8/19
Till now, the only reduction from the module learning with errors problem (MLWE) to the ring learning with errors problem (RLWE) is given by Albrecht et al.et al. in ASIACRYPT 20172017. Reductions fro...
Simulation-Sound Proofs for LWE and Applications to KDM-CCA2 Security
LWE standard model Naor-Yung
2019/8/8
The Naor-Yung paradigm is a well-known technique that constructs IND-CCA2-secure encryption schemes by means of non-interactive zero-knowledge proofs satisfying a notion of simulation-soundness. Until...
In recent years, there has been a proliferation of algebraically structured Learning With Errors (LWE) variants, including Ring-LWE, Module-LWE, Polynomial-LWE, Order-LWE, and Middle-Product LWE, and ...
We give the first construction of statistical Zaps. Our construction satisfies computational soundness and relies on the quasi-polynomial hardness of learning with errors assumpteprint.iacr.orgion.
Many cryptographic schemes have been proposed from learning with errors problems over some rings (Ring-LWE). Polynomial time quantum reduction from the approximating Shortest Independent Vectors Probl...
We construct a 2-message publicly verifiable witness indistinguishable argument system for NP assuming that the Learning with Errors (LWE) problem is subexponentially hard. Moreover, the protocol is `...
Verifying Solutions to LWE with Implications for Concrete Security
lattices learning with errors discrete gaussian sampling
2019/6/21
A key step in Regev's (2009) reduction of the Discrete Gaussian Sampling (DGS) problem to that of solving the Learning With Errors (LWE) problem is a statistical test required for verifying possible s...
Attribute Based Encryption (and more) for Nondeterministic Finite Automata from LWE
Non-determinisitic Finite Automata Attribute based Encrytion Predicate Encryption
2019/6/4
Constructing Attribute Based Encryption (ABE) [SW05] for uniform models of computation from standard assumptions, is an important problem, about which very little is known. The only known ABE schemes ...
Discretisation and Product Distributions in Ring-LWE
Ring-LWE Discretisation Homomorphic Encryption
2019/6/3
A statistical framework applicable to Ring-LWE was outlined by Murphy and Player (IACR eprint 2019/452). Its applicability was demonstrated with an analysis of the decryption failure probability for d...
A refined analysis of the cost for solving LWE via uSVP
learning with errors LWE lattice reduction
2019/5/21
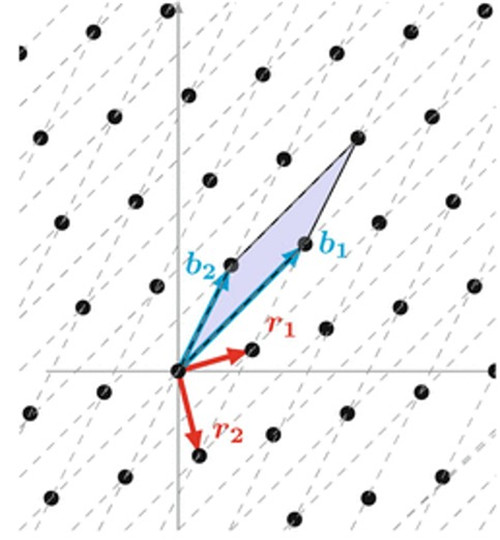
The learning with errors (LWE) problem (STOC'05) introduced by Regev is one of the fundamental problems in lattice-based cryptography. One standard strategy to solve the LWE problem is to reduce it to...
A Central Limit Framework for Ring-LWE Decryption
Ring-LWE Central Limit Theorem δ-subgaussian
2019/5/9
The purpose of this paper is to use a Central Limit approach to develop a statistical framework for analysing ciphertexts in Ring-LWE homomorphic encryption schemes. This statistical framework gives r...
Constant-Round Group Key Exchange from the Ring-LWE Assumption
Group key exchange Ring learning with errors Post-quantum cryptography
2019/4/22
Group key-exchange protocols allow a set of N parties to agree on a shared, secret key by communicating over a public network. A number of solutions to this problem have been proposed over the years, ...

